Cybersecurity for Startups: Detailed Guide to Protecting Your Startup
Launching a new startup in 2025 takes courage, planning, and technological innovation. Pre-planning is crucial for a startup’s success. Even the best ideas may fail due to poor planning and resource management. Cybersecurity is one of the most important yet overlooked factors for startups.
Startups often lack the robust security frameworks of larger companies, making them prime targets for cybercriminals. Implementing strong cyber security practices for startups from the beginning can prevent devastating breaches, regulatory fines, and loss of customer trust. This guide covers everything startups need to know to protect their business from cyber threats effectively.
Do startups need cybersecurity?
Cybersecurity is not just for large enterprises. Startups, often perceived as easy targets, must protect sensitive customer data, financial records, and intellectual property from cyber threats. While no business is completely immune to cyberattacks, industries handling vast amounts of confidential data often face more frequent and costly breaches.
Startups operate in a fast-paced digital world where innovation is key, but so is data security. Many founders focus on product development and scaling, often neglecting cybersecurity until it’s too late. Here’s why cybersecurity for startups should be a top priority:
1. Startups Are Prime Targets for Hackers
Hackers often target startups because they lack robust security infrastructure. One notable example is the Chinese startup DeepSeek attack, which specifically targeted a startup, underscoring how even emerging businesses are vulnerable to sophisticated cyber threats. Cybercriminals look for easy entry points to steal customer data, intellectual property, and financial details. Over 60% of small businesses close within six months of a cyberattack, highlighting the devastating impact of poor security measures.
2. A Single Breach Can Destroy Your Reputation
Data Security of startups is very important. If customer data is compromised, your startup may lose credibility, leading to a decline in users, lost partnerships, and an overall damaged brand image. Companies like Yahoo and Equifax took years to rebuild trust after their massive breaches.
3. Regulatory Compliance is Non-Negotiable
With laws like GDPR, CCPA, and HIPAA, businesses are legally required to protect consumer data. Non-compliance can result in hefty fines, lawsuits, and even bans from operating in certain regions.
4. Cyber Attacks Can Halt Business Operations
A ransomware attack could lock your systems, making it impossible to operate. Without access to your files or software, even a single day of downtime could cause massive revenue losses and disrupt customer trust. “There’s a new risk associated with ransomware infection that could make recovery even more expensive,” according to Forbes Magazine. Cybercriminals are no longer content to encrypt their victims’ data and demand payment for its decryption. Now they’re downloading copies of those files and threatening to release them publicly if the ransom isn’t paid.
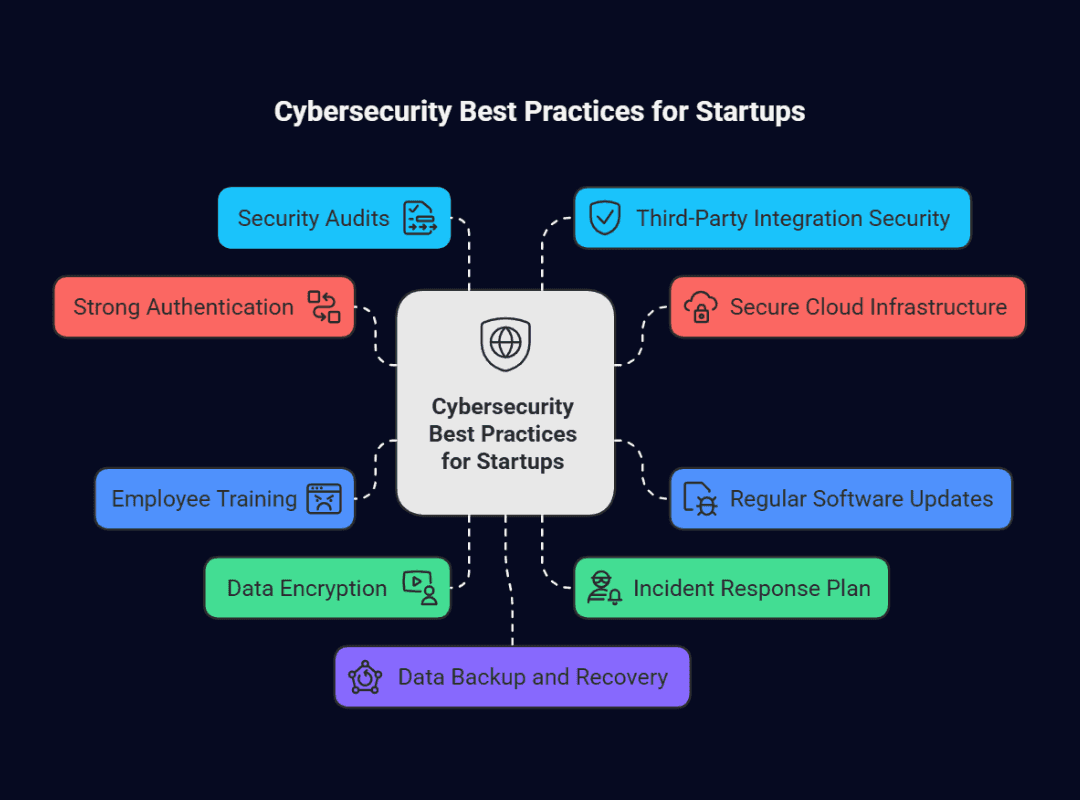
Cybersecurity Best Practices for Startups (With Examples)
1. Implement Strong Authentication and Access Control
Most cyberattacks exploit weak credentials. Using multi-factor authentication (MFA) and role-based access control (RBAC) reduces unauthorized access risks.
Example: A startup implementing MFA ensures that even if an employee's password is compromised, an additional verification step prevents unauthorized access.
2. Secure Your Cloud Infrastructure
Cloud services like AWS and Google Cloud are powerful but vulnerable if misconfigured. Implement data encryption, firewall settings, and least privilege access policies to secure cloud data.
Example: A tech startup encrypts its cloud-stored customer data, ensuring that even if attackers gain access, the data remains unreadable.
3. Regularly Update and Patch Software
Cybercriminals exploit outdated software vulnerabilities. Cybersecurity tips for small businesses are to update operating systems, plugins, and third-party tools.
Example: A SaaS company schedules automatic updates for all software and applications to prevent cybercriminals from exploiting outdated vulnerabilities.
4. Cybersecurity Training for Small Businesses and Startups
Your employees are the first line of defense against cyber threats. Conduct regular training on phishing scams, password security, and data protection.
Example: A startup can conduct regular training sessions for employees to educate them on how to identify phishing scams and other common cyber threats. They can also require employees to report any suspicious activity or incidents immediately and implement strict policies around the use of personal devices for work purposes.
5. Use End-to-End Encryption for Data Protection
Sensitive data should always be encrypted, both in transit and at rest. Implement SSL/TLS protocols for websites and AES-256 encryption for stored data.
Example: A healthcare startup encrypts all patient records to comply with HIPAA regulations and ensure data confidentiality.
6. Develop an Incident Response Plan
Even the best security measures can’t guarantee immunity from cyber threats. Having a clear Incident Response Plan (IRP) helps your startup recover quickly.
Example: A fintech startup creates a step-by-step response plan for data breaches, ensuring swift action to minimize damage and notify affected users.
7. Conduct Regular Security Audits and Penetration Testing
Routine security audits and penetration testing (ethical hacking) can uncover vulnerabilities before hackers exploit them.
Example: A startup hires a cybersecurity firm to perform annual penetration tests, identifying and fixing security weaknesses before they become risks.
8. Secure Third-Party Integrations
A 2024 study by the Ponemon Institute and IBM revealed that 53% of organizations experienced data breaches linked to third-party vendors
This results in an average remediation cost of $7.5 million. Startups often use third-party services for payments, analytics, and marketing automation. Ensure vendors comply with industry security standards before integrating them.
Example: Suppose your startup partners with a third-party vendor for payroll processing. Before finalizing, conduct a risk assessment of their security measures. Require regular security reports and include specific protections in your contract, such as data policies, incident reporting, and security audits. These steps help mitigate risks and keep your data secure.
9. Backup Data Regularly and Implement Disaster Recovery Plans
Regular backups ensure business continuity in case of cyberattacks or accidental data loss. Store encrypted backups in multiple locations and test recovery plans periodically.
Example: A startup implements a backup strategy with regular, secure backups and routine testing to ensure functionality and data integrity. Learn from the Microsoft CrowdStrike outage for valuable insights on disaster recovery planning.
10. Invest in a Cybersecurity Insurance Policy
Cyber insurance can help cover legal costs, data recovery expenses, and regulatory fines in case of an attack. It’s a crucial safety net for startups.
Example: A growing tech company purchases cyber insurance to mitigate financial risks, ensuring they recover from an attack without major financial losses.
Final Thoughts: Prioritize Cybersecurity for Startups
Cybersecurity isn’t an afterthought; it’s a necessity. By implementing these best practices, startups can reduce the risk of cyber threats, build customer trust, and stay compliant with regulations.
Are you a cybersecurity vendor looking to connect with decision-makers in the startup space? Execweb is the leading cybersecurity marketing platform that connects vendors with 400+ CISOs and security practitioners. Our platform facilitates one-on-one virtual meetings, allowing vendors to showcase their solutions and build valuable business relationships
Join a network of top security vendors already leveraging Execweb to grow their business and connect with the right buyers. Want to learn more? Email us at contact@execweb.com or call us to explore how Execweb can help you reach your target audience in the cybersecurity space.






Comment